How to Jailbreak iOS 9 – iOS 9.0.2 using Pangu Jailbreak
Pangu team just surprised us by releasing Pangu jailbreak for iOS 9 – iOS 9.0.2, the first jailbreak for iOS 9 and also for iPhone 6s, iPhone 6s Plus. Here’s how to jailbreak your device running on iOS 9, iOS 9 or iOS 9.0.2 using Pangu jailbreak.
Some important points before you proceed:
- Pangu9 jailbreak tool can jailbreak iOS 9, iOS 9.0.1, iOS 9.0.2.
- Pangu supports following iOS 9 – iOS 9.0.2 devices:
- iPhone 6s, iPhone 6s Plus, iPhone 6, iPhone 6 Plus, iPhone 5s, iPhone 5c, iPhone 5, iPhone 4S
- iPad Air 2, iPad Air, iPad 4, iPad 3, iPad 2
- iPad mini 4, iPad mini 3, iPad mini 2, iPad mini
- iPod touch 6G, iPod touch 5G
- Pangu 9 is an untethered jailbreak.
- Pangu 9 is a free jailbreak tool.
- You need a computer (Mac or Windows PC) to use the Pangu Jailbreak. Mac users can check our guide on how to jailbreak iOS 9 – iOS 9.0.2 using Pangu Jailbreak for Windows.
- Use iCloud or iTunes to back up any and all personal information that you need to keep safe. The jailbreak has been reported to be working in most cases, but on the off chance something goes wrong, it’s a good idea to have an escape plan.
- Disable any Anti-virus programs or firewalls that could prevent Pangu from connecting to the internet.
- If you’re on the fence and not sure if you should jailbreak your device, then check our post on some of the tops reasons to jailbreak iOS 9 – iOS 9.0.2.
How to Jailbreak iPhone, iPad and iPod touch on iOS 9 – iOS 9.0.2 using Pangu Jailbreak
Follow these steps to jailbreak your iPhone, iPad and iPod touch on iOS 9 – iOS 9.0.2 using Pangu jailbreak.
Step 1: Download the latest version of the Pangu jailbreak our Download Pangu Jailbreak page. Pangu jailbreak is a free jailbreak tool. It should not prompt you to enter a registration code.
Step 2: Connect your device to your computer using the USB cable.
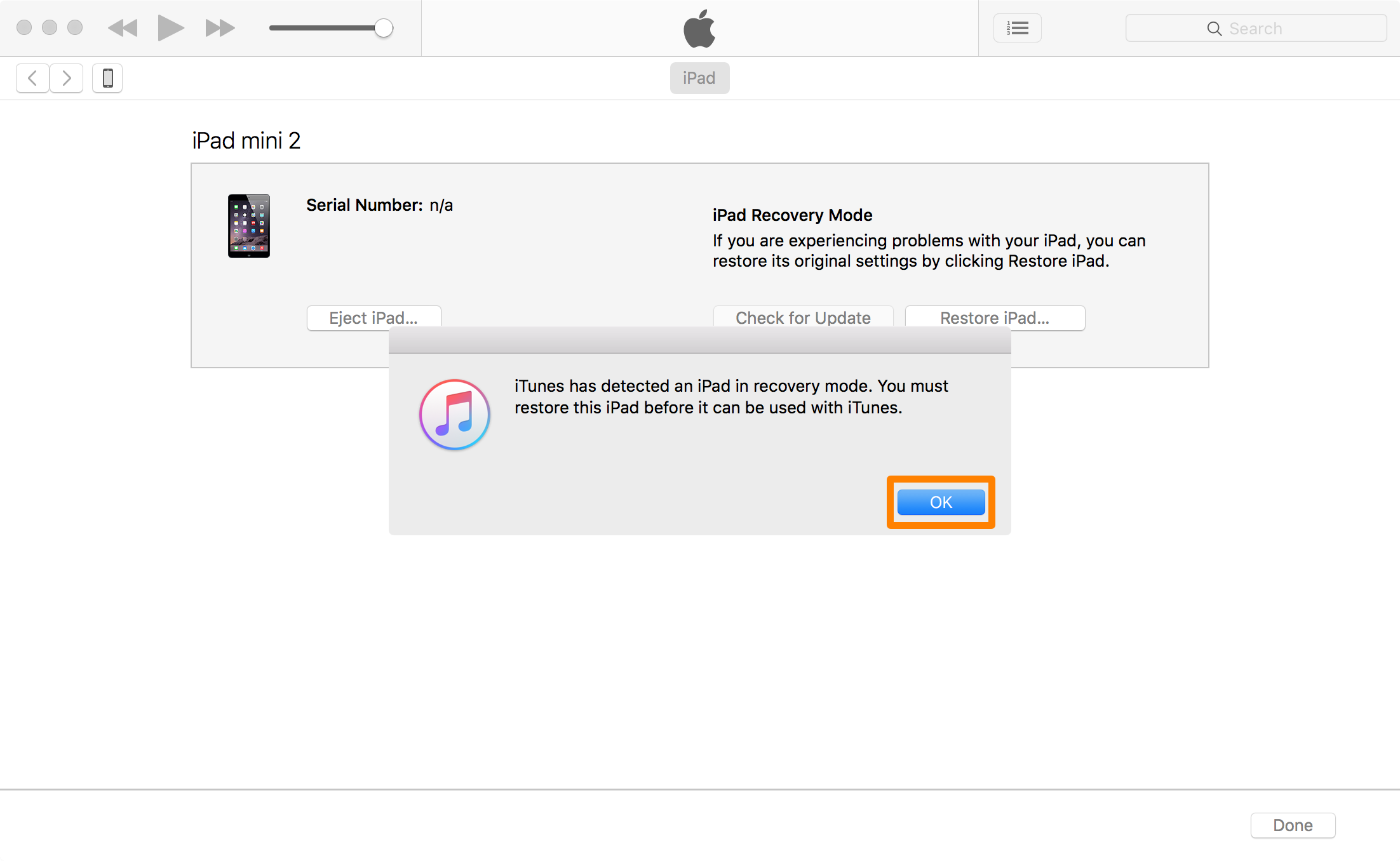
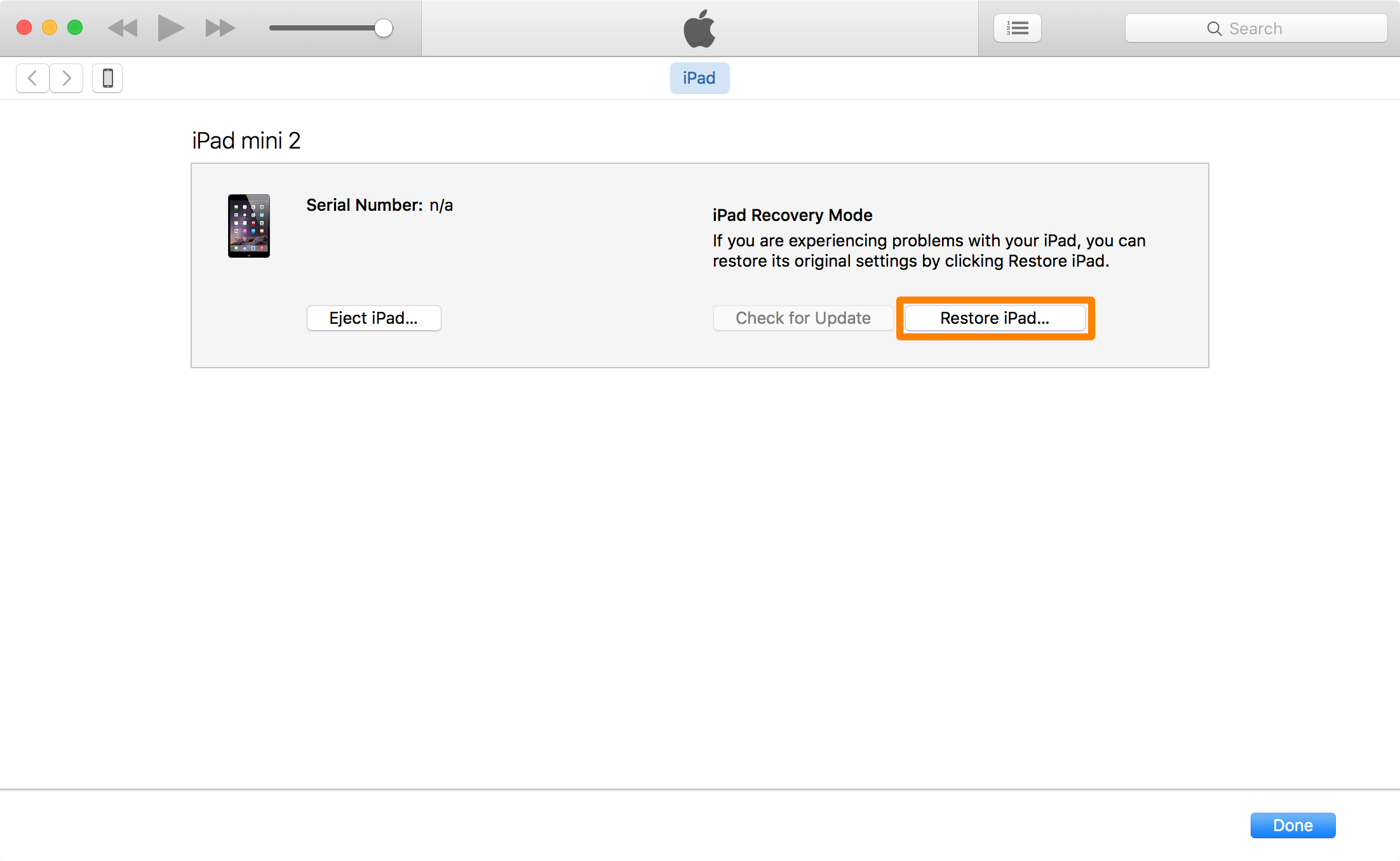
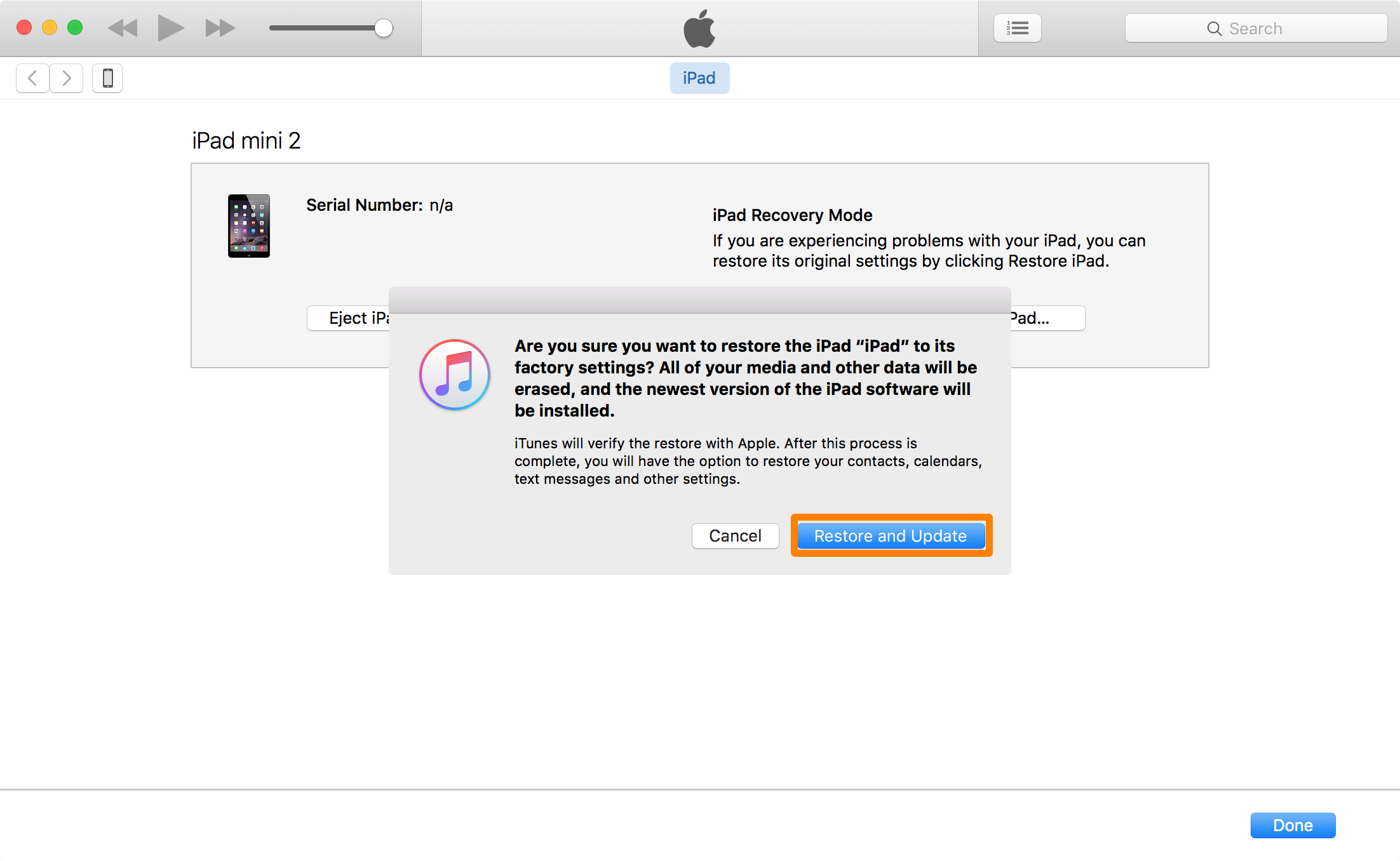
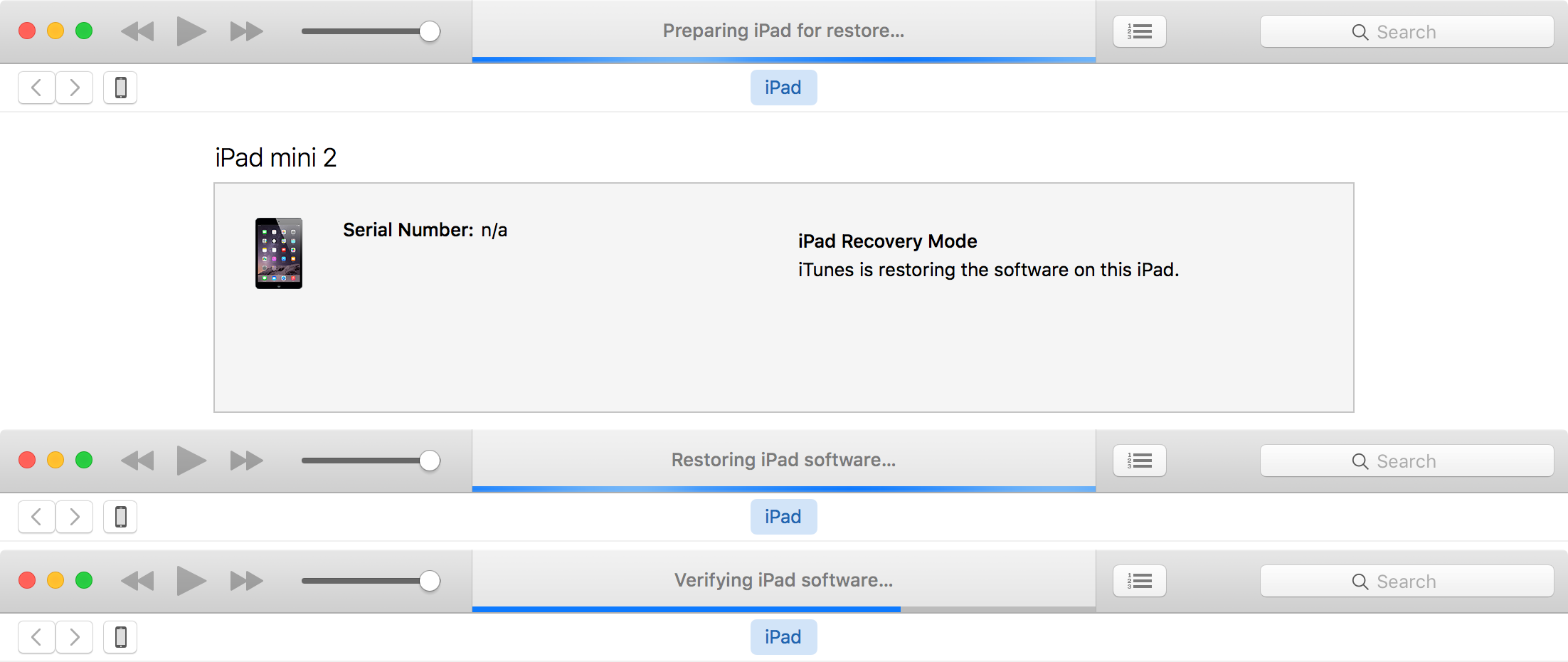
Step 3: Take a backup of your device using the latest version of iTunes. After you’ve taken the backup, close iTunes. Also close Xcode if you’ve it open.
Step 4: Disable Passcode from Settings > Touch ID & Passcode, turn off Find my iPhone from Settings > iCloud > Find my iPhone, and enable Airplane mode.
Step 5: Please launch the Pangu 9 application that you had downloaded in step 1 as an Administrator. Right Click on the Pangu exe and select the “Run as Administrator” option.
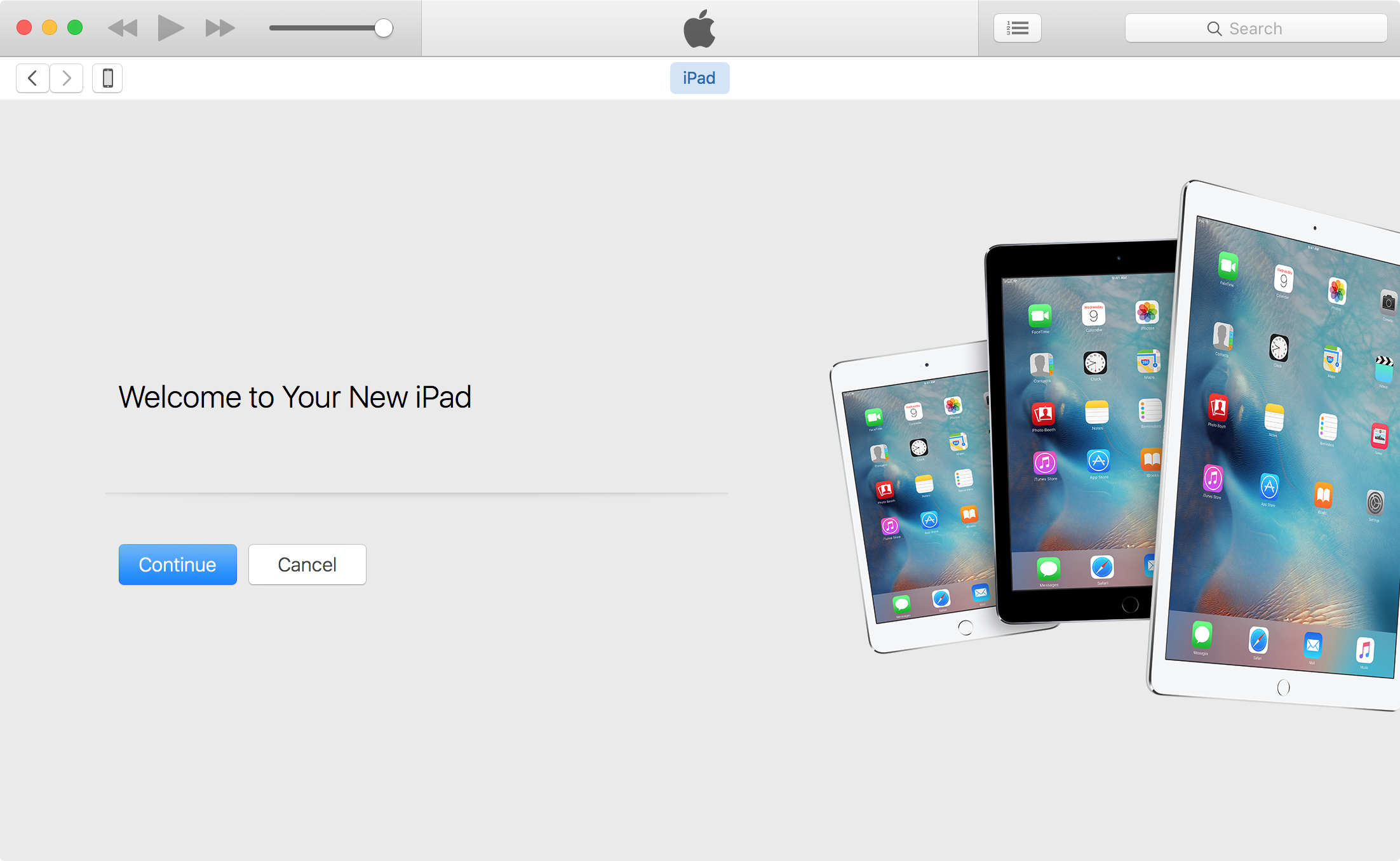
Step 6: Pangu will take some time to detect your device. Once that is done, click on the blue Start button.

Step 7: Click on Already Backup button to proceed to the jailbreak.

Step 7: At 55%, it will reboot your device.
Step 8: At 65%, it will prompt you to enable AirPlane mode again after your device has rebooted.
Step 9: At 75%, it will then prompt you to unlock your device, and run the Pangu app. Launch the Pangu app from the Home screen. If you can’t find the app the try searching your device for “Pangu”. It also installs the WWDC app but you can ignore it. The Pangu and the WWDC app will be removed when your device is successfully jailbroken.

Step 10: Next, it will prompt you to tap on the Accept button, to give access to the Photos app. Next tap on Allow when you get a popup on your device. It is not clear why it needs access to the Photos app, we’ll update the post when we get more information.

Step 11: Wait for the progress bar to complete. Your iPhone or iPad will reboot.
Step 12: Once the process completes, the Pangu tool will tell you that your device is “Already Jailbroken”. You should see the Cydia icon on your home screen. Please don’t forget to disable AirPlane mode before launching Cydia. Cydia will take some time “Preparing filesystem” when you launch it for the first time. It will exit after it is done, and respring your device.









 Apple iPhone 7 review blog: Here’s what we think of the new phone.
Apple iPhone 7 review blog: Here’s what we think of the new phone.